by Koh Teng Teng
Share
Share
MAS Cyber Resilience Governance 2026: What Financial Institutions Should Take Note Of
As financial services remain a prime target for cyber criminals and advanced persistent threats (APTs), a successful attack on a financial institution (FI) can disrupt the delivery of financial services and erode public confidence. This Advisory summarises practical governance-focused steps to protect against contemporary threats and to address control gaps and weaknesses that have led to breaches in the past year.
In several recent incidents, organisations had effectively deprioritised cybersecurity in favour of business performance and convenience, leaving critical IT infrastructure exposed. The Monetary Authority of Singapore (MAS) has reinforced that cyber resilience is now a governance issue — not merely an IT issue — and expects boards and senior management to demonstrate clear oversight and risk ownership.
Boards and Senior Management should therefore:
- Authorise and review the institution’s cyber risk management framework, ensuring it aligns to the organisation’s risk appetite and business strategy.
- Approve trade-offs between business objectives and security controls, and require documented evidence when risks are accepted.
- Empower the Chief Information Security Officer (CISO) and relevant functions with resources, authority and direct reporting lines to enable effective governance and visibility of risks.
- Require regular, concise board-level reporting on cyber risks, controls, incidents and remediation progress — with clear escalation triggers.
- Ensure third-party and vendor arrangements are covered by governance and oversight arrangements proportionate to the institution’s risk exposure.
For institutions conducting governance reviews, Alder offers practical support to align policies and documentation with evolving MAS expectations — including compliance policy outsourcing and risk management assistance. See Alder’s compliance support services for more details.
Cyber Risk Governance
FIs must establish a robust governance structure and a risk management framework that places cyber resilience squarely within board and senior management accountabilities. Key decisions that trade off business objectives against security controls should be formally approved by Senior Management and, where appropriate, authorised by the Board. MAS expects institutions to move beyond a compliance-only mindset and adopt a consistently risk-focused approach to govern cyber risks in line with the institution’s risk appetite and business strategy.
CISOs, Heads of IT Security or equivalent functions should be empowered with clear authority, direct access to the Board or Board committees, and sufficient resources and competencies to discharge their duties effectively. Institutions must document the CISO’s mandate, reporting lines and delegated authorities, and evidence that those arrangements are exercised in practice.
Leverage the Three Lines of Defence (3LoD) to make responsibilities explicit and to provide assurance that controls operate effectively. Typical governance expectations include:
- Board / Executive: set strategy, approve risk appetite, and receive concise, regular cyber risk reports (including incident metrics and remediation status).
- First Line (Business & IT): own and operate controls; maintain inventories and implement mitigations; produce operational evidence and attestations.
- Second Line (Risk & Compliance): define policy, set standards, monitor control effectiveness, and provide independent oversight of vendor and third‑party risk.
- Third Line (Internal Audit): provide independent assurance over the adequacy and effectiveness of the 3LoD arrangements and remediation evidence.
Recommended governance artefacts to review and update as part of a governance refresh include: governance charters and committee terms of reference; cyber risk appetite statements; CISO role and delegation documents; incident escalation matrices; third-party oversight policies; and board reporting templates. Suggested board-level KPIs for ongoing oversight include frequency of incidents, mean time to detect and respond, percentage of critical remediation closed within SLA, and the status of third-party risk reviews.
For practicality, a simple board paper checklist might require: (1) clear statement of residual cyber risk and rationale for any risk acceptance; (2) summary of recent incidents and lessons learnt; (3) remediation progress versus previous board directions; (4) resource or budget implications; and (5) recommended decisions or approvals sought. Where organisations prefer external help to accelerate documentation or to operate some elements of oversight, Alder’s compliance policy outsourcing and risk management services can provide pragmatic support aligned with MAS expectations.
Cyber Security Practices
Threat actors, including APTs, commonly exploit weaknesses in basic cyber hygiene to gain an initial foothold and move to critical systems. For a governance audience, these technical controls should be framed as areas where Boards and Senior Management require clear policies, documented assurance and timely reporting so that risks to systems and services are visible and managed in line with the institution’s risk appetite.
Below are the core control areas MAS highlights, each followed by the governance evidence Boards should expect to receive (Control → Governance evidence):
- IT asset, inventory and configuration management: maintain an up‑to‑date inventory of hardware, software, network and cryptographic components, including versions, configurations, connectivity and dependencies.
- Governance evidence for Boards: an owner-assigned asset register with change logs (monthly reconciliation), dated network diagrams and configuration baselines, and a vulnerability-to-patch register showing remediation timelines and SLA compliance. Require periodic attestations from the first line that inventories and configuration records are complete and reconciled.
- Network segmentation and access control: segregate production networks by function/criticality and enforce network access controls; where feasible, use separate administrative networks for management access.
- Governance evidence for Boards: segmentation rationale and design diagrams, exception logs for cross‑zone access, results from segmentation tests or traffic reviews, and documented approvals for any out‑of‑band administrative access. Request periodic metrics on blocked unauthorised connections and any observed lateral movement attempts to assess residual risk and the institution’s security posture.
- Privileged identity and access management (IAM): grant administrative and privileged accounts on a need‑to‑use basis, secured with centralised privileged access management, role‑based controls and multi‑factor authentication.
- Governance evidence for Boards: a current privileged‑account inventory, access‑request and approval records, periodic privileged‑access reviews, and exception/justification logs for elevated access. Boards should ask for summaries of privileged activity reviews and any detected misuse, along with remediation actions and timelines.
- Threat detection and mitigation: deploy detection capabilities (for example endpoint and network detection solutions such as EDR/NDR) to identify suspicious activity and enable containment and remediation.
- Governance evidence for Boards: detection coverage maps, alert-to-investigation timelines, examples of automated containment actions, and regular summaries of detected threats by severity. For non‑technical directors, include plain‑English explanations of detection scope and any blind spots, plus a plan to remediate them.
- Centralised security monitoring: consolidate logs and events into centralised monitoring to correlate incidents and produce timely alerts.
- Governance evidence for Boards: monitoring platform coverage and ingestion health, mean time to detect (MTTD) and mean time to respond (MTTR) metrics, tickets linked to investigations, and examples of how monitoring outputs informed incident containment. Boards should also see vendor oversight reports where monitoring is outsourced to providers.
Practical governance recommendations and examples
- Turn each control into an assurance‑driven artefact: policy → owner → control evidence → testing schedule → board reporting cadence. For example, require quarterly attestation of the IT asset register and monthly vulnerability‑remediation reporting.
- Ask for control lifecycle evidence: when controls were designed, last tested, next scheduled test, and remediation status. This shifts discussion from “we have controls” to “we can prove they work”.
- Where controls are provided by third parties, demand provider SLAs, testing reports and independent assurance — and ensure those are included in vendor oversight reporting to the Board.
- Use short governance‑facing visuals: a two‑column table mapping each control to the expected governance evidence, and simple icons (inventory, segmentation diagram, key for IAM, shield for detection, dashboard for monitoring) to improve visibility in board packs.
Short governance examples (for board papers)
- IT asset example: “Monthly asset reconciliation completed; 98% match rate; 2 unaccounted devices quarantined.”
- Segmentation example: “Segmentation test conducted — lateral movement prevented in 5/6 simulated scenarios; exception logged for application X with remediation plan.”
- Privileged access example: “Privileged access review completed; 3 accounts removed; 1 exception approved with compensating controls.”
- Detection/monitoring example: “EDR detected anomalous login pattern; automated containment executed; incident contained within 30 minutes. MTTR improved by 20% QoQ.”
How Alder can help
Boards and Senior Management often need to translate these technical control areas into tangible governance artefacts and assurance reporting. Alder provides pragmatic support — from drafting governance documentation and board reporting templates to conducting gap assessments of controls, processes and vendor oversight. Where organisations prefer external execution, Alder can assist in structuring service provider agreements and evidence flows so the Board retains visibility and control.
Cyber Security Assurance & Testing
FIs should conduct regular security testing to verify the effectiveness of controls and to provide the Board and Senior Management with verifiable assurance that cyber risk is being managed in line with the institution’s risk appetite. Testing is not solely a technical exercise: the governance outcome matters — evidence of tests, remediation progress, risk acceptance and reporting triggers should all be visible to decision‑makers.
Recommended assurance activities (technical activity → governance output):
- Vulnerability assessments — output: prioritised vulnerability register, remediation timelines and SLA compliance reports for Board review.
- Penetration testing and adversarial simulations — output: executive summary of exploitable weaknesses, residual risk statements, and remediation attestations.
- Table‑top exercises and crisis simulations — output: assessment of incident response readiness, escalation effectiveness, and required updates to incident response plans and playbooks.
A sample template is available at the end of the article for effective board oversight.
Key KPIs and metrics for Board-level visibility
- % of critical/high vulnerabilities remediated within SLA
- Mean time to detect (MTTD) and mean time to respond (MTTR)
- Number of security incidents escalated to Senior Management/Board
- Percentage of systems covered by testing and monitoring
- Third‑party provider testing and assurance completion rates
ASM vs Bug Bounty — governance checklist
- ASM is suitable when the priority is continuous discovery and inventory of externally facing systems; require provider SLAs, regular reports and evidence ingestion into monitoring platforms.
- Bug Bounty Programmes are appropriate to crowdsource testing against production assets where controlled disclosure is managed; require clearly defined scopes, triage processes and payment/engagement terms with providers.
- For either service, ensure contractual obligations for confidentiality, remediation timelines, evidence sharing and audit rights are documented and reported to the Board as part of vendor oversight.
Escalation and integration into governance
- Define explicit escalation thresholds: when testing finds critical exploitable vulnerabilities, remediation plans and risk acceptances must be escalated to Senior Management and the Board.
- Ensure post‑exercise after‑action reports feed into the risk management framework and change control processes so that testing outcomes drive sustained improvement in controls and processes.
Standards and technology risk alignment
Align testing and assurance activities to recognised standards and the MAS Technology Risk Management Guidelines to ensure consistency of approach, comparability of results and regulatory compliance. Where testing is outsourced to providers, include evidence of provider qualifications, scope, and independent validation in board reporting.
FIs are advised to read this Advisory alongside the MAS Notice on Cyber Hygiene and the MAS Technology Risk Management Guidelines, and to implement measures proportionate to the size, scale and criticality of their systems and operations to strengthen cyber resilience. The Monetary Authority of Singapore (MAS) expects institutions to apply the same rigour to third‑party arrangements where technology or digital services introduce comparable risk.
Summary of MAS expectations for Boards and Senior Management
- Institutions must treat cyber resilience as a governance responsibility and demonstrate active oversight of technology risk, controls and monitoring.
- Adopt a risk‑based approach aligned to applicable standards and the institution’s risk appetite; document decisions where risks are accepted and escalate material issues promptly to Senior Management and the Board.
- Ensure compliance and vendor arrangements include contractual obligations for testing, evidence sharing and remediation timelines so the Board retains visibility over outsourced functions and providers.
- Maintain up‑to‑date documentation and reporting that supports timely response to incidents and continuous improvement of the institution’s security posture.
Immediate next steps for Boards
- Commission a governance gap assessment focused on cyber resilience and technology risk.
- Review and, if necessary, update the CISO’s mandate, reporting lines and resourcing to ensure effective oversight.
- Confirm vendor governance: ensure critical providers deliver testing evidence, monitoring reports and agreed SLAs.
- Agree board reporting cadence and escalation thresholds for cyber incidents and test outcomes.
If your firm is reviewing whether its governance, risk management, and compliance documentation remains aligned with evolving MAS expectations, Alder can assist with practical gap assessments and framework support. Learn more about Alder’s compliance policy outsourcing and governance services here.
Sample Template for hollistic assurance testing:
| Activity Suggested | Frequency | Owner | Board reporting trigger | Evidence |
|---|---|---|---|---|
| Vulnerability assessment | Quarterly/Annually (risk-based) | IT / 1LoD | Critical findings or overdue remediations | Prioritised register, remediation status |
| Penetration test / Red team | Annually or upon major change | Security function | High-severity exploitability | Exec summary, remediation plan |
| Table-top exercise | Annual | Security Provider | Significant gaps in playbook | Lessons learned, revised plans |
| ASM / external scanning | Continuous / Periodic | Security Provider | New exposed assets or critical findings | ASM discovery reports, closure evidence |
| Bug bounty programmes | Ongoing (campaigns) | Security Provider | Critical vulnerabilities reported | Validated reports, fixes, disclosure handling |
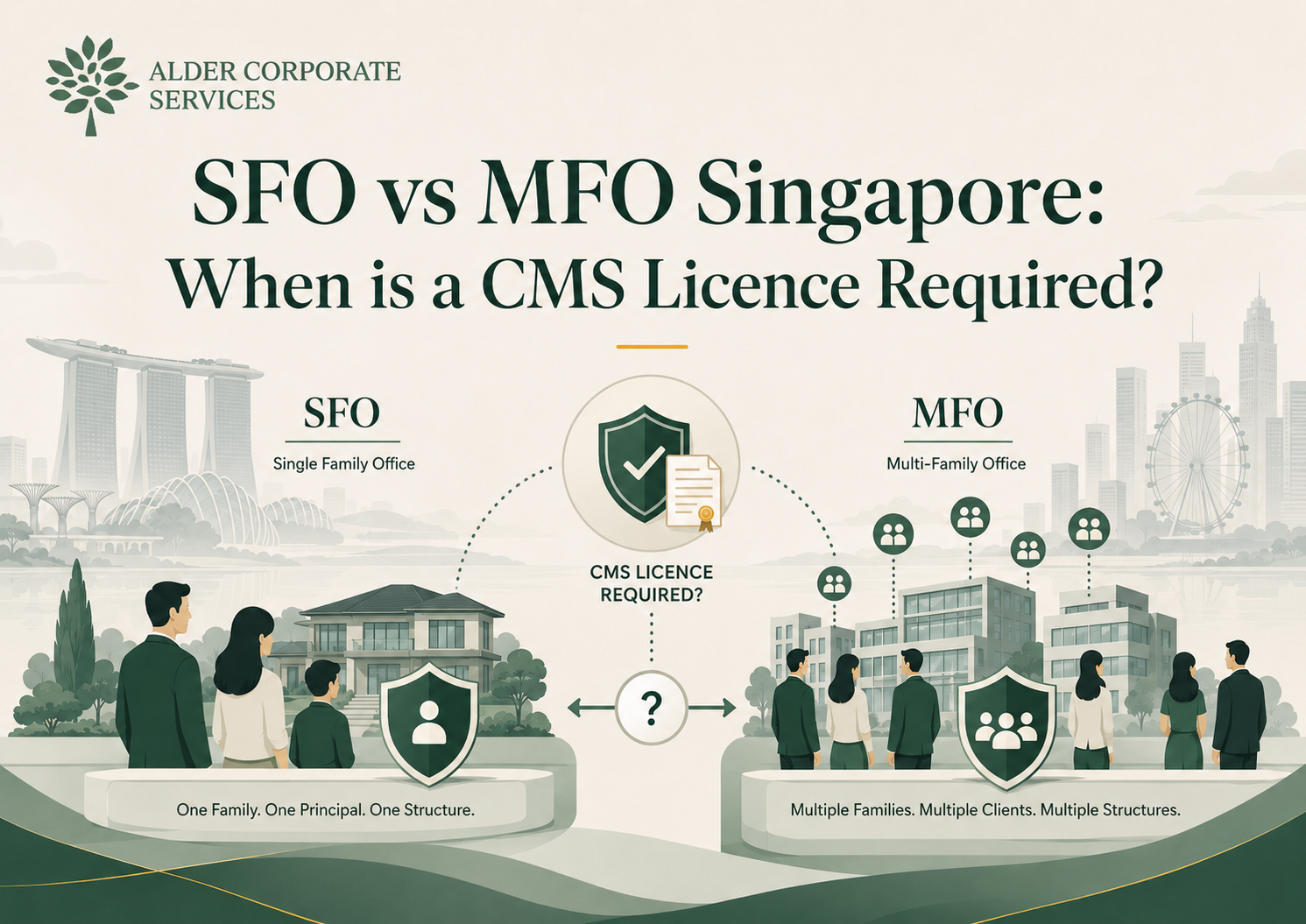
Compare SFO vs MFO Singapore models. Understand when a CMS licence Singapore is mandatory for fund managers and identify key MAS regulatory licensing triggers.
Explore how an Outsourced Compliance Officer (OCO) provides shared expertise for fund managers to meet MAS requirements and SFA compliance arrangements.
Navigating CMS licensee compliance: Our guide unpacks MAS guidelines and CMS licensee responsibilities for financial institutions in Singapore.